How do cybercriminals use your data against you?
Social engineering continues to increase. Hackers are using a variety of sophisticated ways to obtain your sensitive information. A source that is not immediately obvious is the data hidden in shared documents such as comments, username, editing histories, document properties and even GPS coordinates attached to images.
Join Clearswift webinar to discover how attackers are harvesting this information to build a profile of your organisation and the people in it to mount targeted attacks.
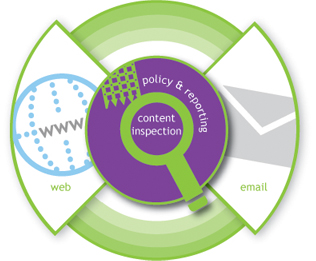
Clearswift will also explain how you can use their solutions to reduce the risk of such attacks, protecting your organisation’s business interests and reputation from unintentional data disclosure.